Cybercrime has become one of the biggest risks to the care sector and too many organisations still don’t see it coming.
Whether you’re running an NHS Trust, a care home, or a home care agency, you are now a target for cybercriminals. And the consequences go far beyond a few IT glitches.
- Missed care calls.
- Lost patient data.
- ICO fines.
- Fake invoices paid out.
- CQC enforcement.
- Lost contracts.
It’s no longer enough to say, “We’ve got Cyber Essentials,” or “We’ve completed the DSPT.”
Because when things go wrong, it’s not the badge that protects you — it’s your people.

Real UK Examples: NHS, Care Homes & Domiciliary Providers
Synnovis NHS Lab Hack (2024)
- Ransomware group Qilin shut down key NHS pathology services.
- 1,000+ surgeries and 2,000 appointments cancelled.
- 400GB of patient data stolen.
- Cost: £32.7 million — seven times their profit.
HCRG Care Group (2025): Domiciliary and Community Care
- Provides home and NHS community care across the UK.
- Medusa ransomware encrypted 50TB of data.
- $2 million ransom demand; legal fallout continues.
Advanced Software Breach (2022): Affecting Care Homes & Agencies
- Staffplan and Caresys systems used by hundreds of providers were attacked.
- 83,000+ people’s data compromised, including 890 vulnerable clients.
- Systems down for weeks.
- Cost: £27.6 million + £3 million ICO fine (pending)

“But It Was Our IT Provider’s System: Are We Really Liable?”
✅ Short answer: Yes –and here’s why.
If your provider is breached, they may be fined.
But you are the data controller – you still:
- Chose the supplier
- Stored sensitive data
- Gave staff access
- Failed to assess the risks properly (if applicable)
If your staff accidentally send personal data to a scammer, or if you can’t show staff were trained – you’re responsible.
Fines aside, you’ll still face:
- Reputational damage
- CQC scrutiny
- Contract loss
- Client complaints
- Legal fees
- Weeks of operational chaos
So yes — you absolutely need to care.
The Real Financial Risks for Care Providers
- Fake invoice scams
Scammers impersonate a supplier and change bank details.
You pay £5,000 and it’s gone. - Staff email hacks
A hacked inbox sends out payroll or client data.
You face an ICO breach report and possible compensation claims. - Data sent to the wrong person
A manager emails client details to the wrong contact.
You now have a reportable breach and a safeguarding risk. - Systems offline due to ransomware
You miss care calls. Medications aren’t recorded.
You still have to pay staff and answer to CQC. - Lost NHS or council contracts
Breach or non-compliance with DSPT or CE could lose you tenders worth hundreds of thousands.
🛡️ Cyber Essentials: What It Does (and Doesn’t) Do
| ✅ Cyber Essentials (CE) | ✅ Cyber Essentials Plus (CE+) |
|---|---|
| Basic security self-assessment | Audited version with external testing |
| Covers 5 technical areas | More robust and often required for NHS contracts |
| Helps prevent basic attacks | Proves systems are actually secure |
| Starting point, not a full solution | Stronger credibility with NHS and commissioners |
❌ What Neither of Them Covers:
- Staff behaviour (e.g. clicking scam emails)
- Email impersonation
- Data sharing over WhatsApp or USBs
- What to do when there’s a breach
- Ongoing cyber awareness or organisational culture
Cyber Essentials is like putting a lock on your door.
But your biggest vulnerability is usually the person holding the keys.
What Is the DSPT and Does It Actually Work?
The Data Security and Protection Toolkit (DSPT) is a mandatory online self-assessment for any provider handling NHS data, using NHSmail, or receiving NHS funding.
You must complete it every year to:
- Keep access to NHS systems
- Keep NHS contracts
- Prove you’re GDPR-compliant
✅ It can be effective when used properly:
- Highlights data risks and process gaps
- Encourages board-level conversations
- Supports CQC “Well-led” evidence
- Helps you avoid or reduce ICO fines
❌ But yes it can become a tick-box exercise if:
- One person completes it alone
- Uploaded policies are never read
- Training isn’t actually delivered
- It’s filed once a year then ignored
DSPT works if you treat it as part of your governance and leadership — not just IT admin.
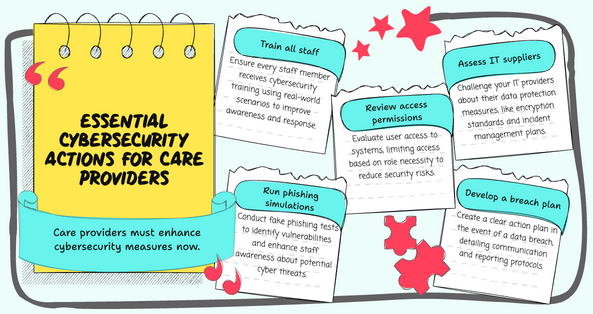
What Care Providers Should Be Doing Now
Whether you’ve got Cyber Essentials or DSPT status — you still need to act.
✅ 1. Train all staff, at every level
- Use real examples: fake bank details, phishing emails, social engineering
- Make cyber awareness part of induction and refreshers
✅ 2. Run phishing simulations
- Send fake “test scams” to see who clicks and where the gaps are
✅ 3. Review who can access what
- Does everyone need access to every system? Limit by role.
✅ 4. Assess and challenge your IT suppliers
- Do they encrypt backups? Do they have incident response plans? You should know.
✅ 5. Have a breach plan
- If something happens, who do staff tell? Who contacts the ICO? What’s the message to families?
Final Word: If You Care for People, You Must Care for Their Data
Cyber breaches aren’t just technical events — they are human, operational, and financial crises.
Even if you weren’t the one hacked, you will still face the consequences.
When a phishing email tricks your finance lead…
When your care coordinator sends a spreadsheet to the wrong inbox…
When the regulator asks if your team was trained…
Your answer is your protection. Or your liability.
Need help training your team or strengthening your cyber readiness?
We provide tailored workshops, phishing simulations, and DSPT/Cyber Essentials support — designed for real-world care providers.
📩 Let’s protect your people, your contracts, and your bottom line.
